Government Services
Federal Contractor
NexThreat offers an array of services to help organizations manage their sensitive data. We're a partner you can depend on. The reality of today's cyber-threat environment requires sole dedication to protecting private data and expertise in privacy compliance, data analysis, and cloud migration.
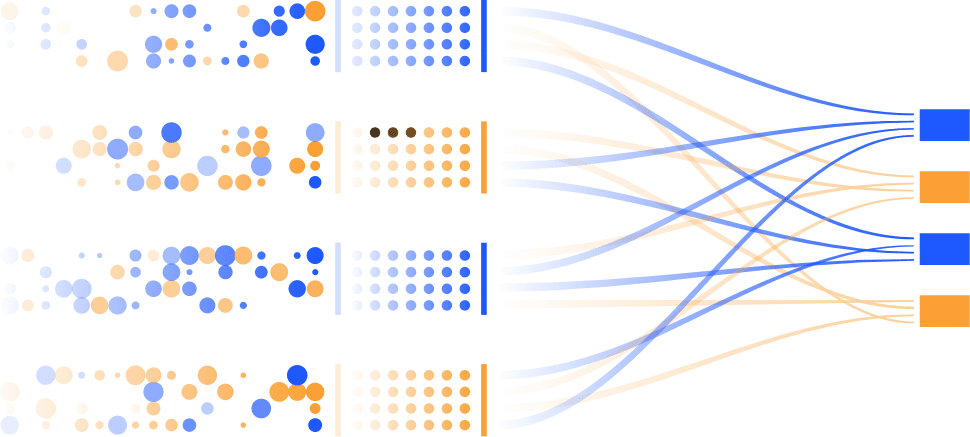
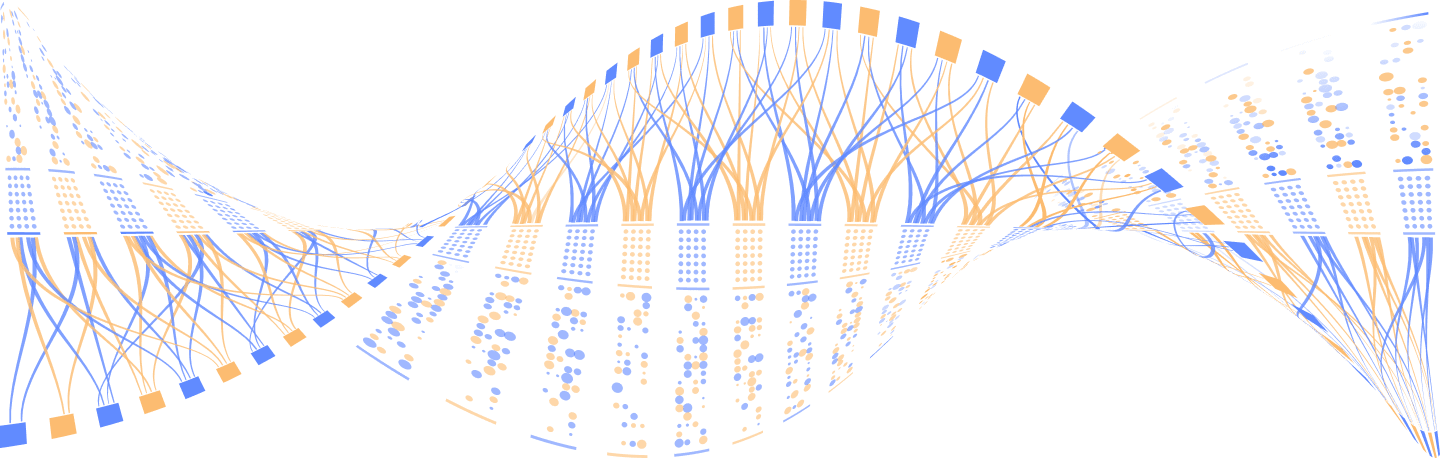
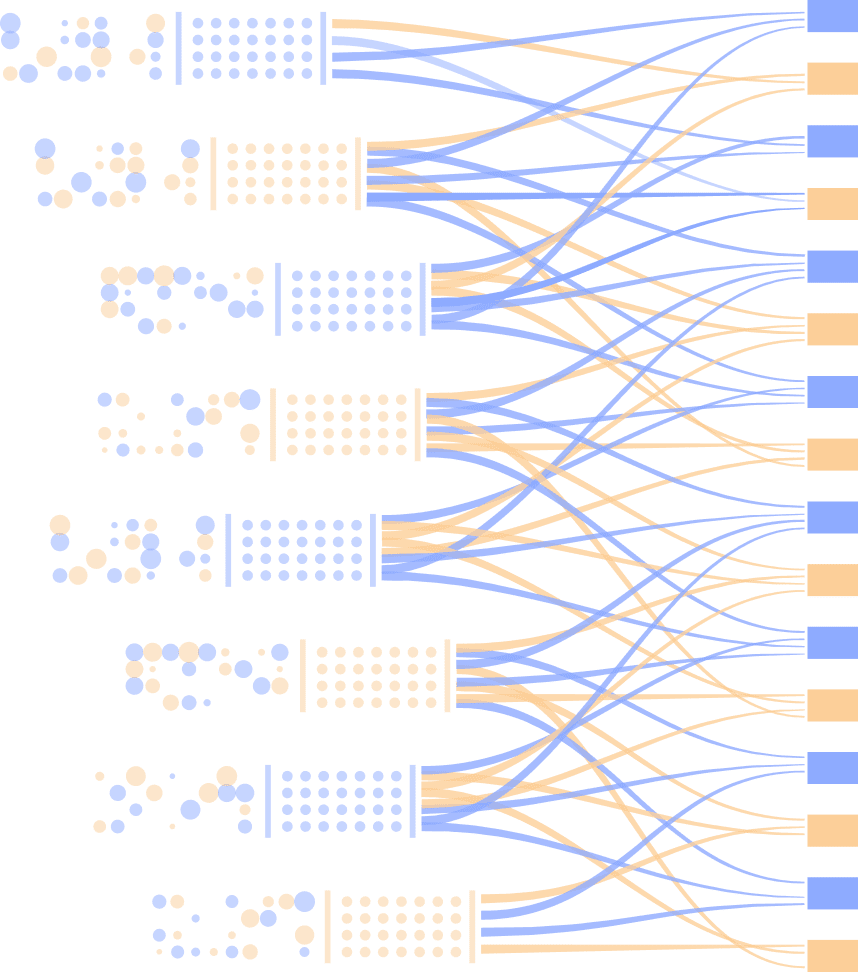
This is how we do it: A security team with engineers and intelligence experts is coordinated to use advanced data mining and analytical techniques from advanced AI that detects failures and vulnerabilities, forcing attackers into advanced frustration and sending them on their way. Then, where possible, we track and report their activity.
We know your company has its core function, and through all of our security operations, you will have the flexible digital environment you deserve. With NexThreat Compliance Automation, enterprises can be secure and comply with new regulations without sacrificing platform performance.